Alerts and applied intelligence are a suite of tools and features that proactively notify you when things go wrong... right when they're starting to go wrong.
Want to try Alerts & AI? Join us! It's free... forever!
Already have an account? Login.
Alerts lets you define the conditions in your system you want to be notified about, letting you focus on the things you care about most.
Applied intelligence is a machine-learning engine that reduces alert noise, correlates incidents, automatically detects anomalies, and provides root cause analysis. Not only that, it enriches your notifications with metadata to give you greater context of what's happening when you are notified.
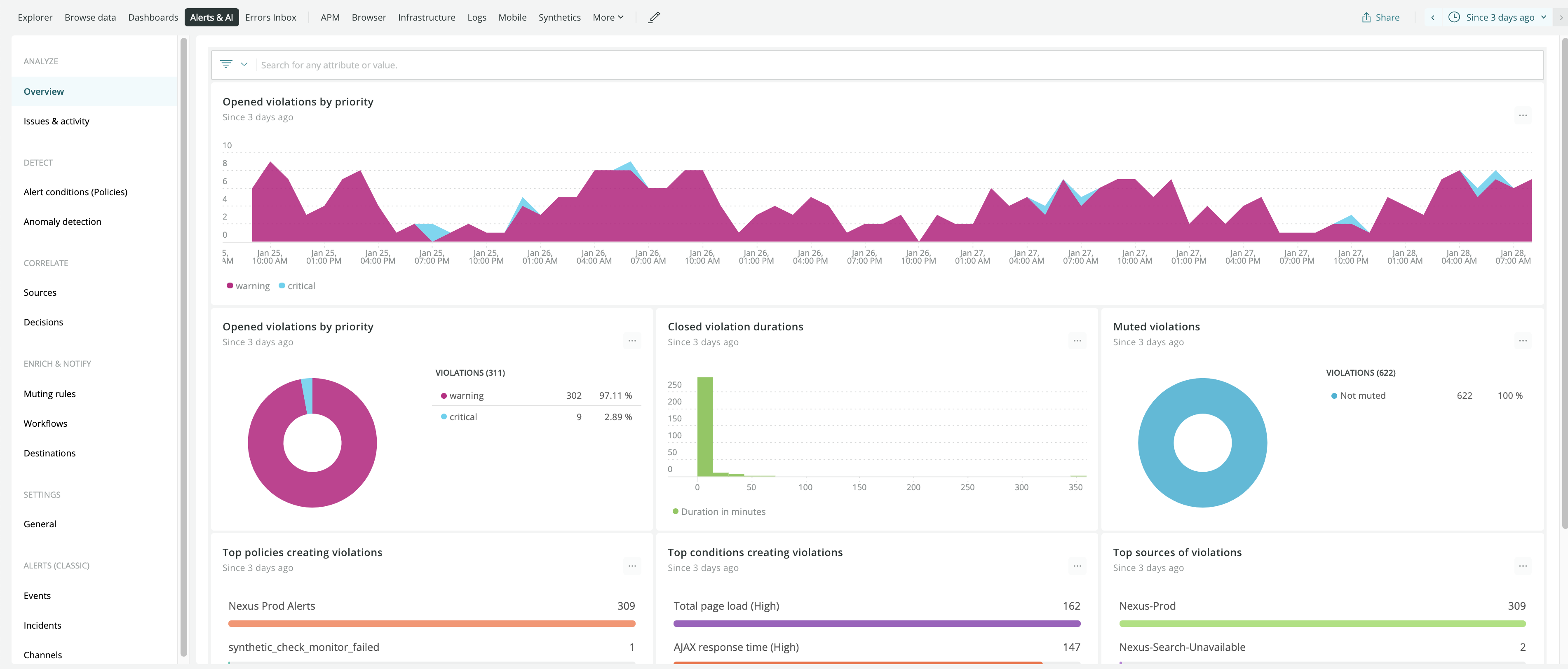
one.newrelic.com > Alerts & AI: You can use the overview summary page to quickly review your issues and incidents.
In the New Relic UI, Alerts & AI is divided into several sections, each unlocking different features. Check out the section explanations below to learn how these features can meet your needs.
Analyze your issues, incidents, and anomalies
Use the analyze features to scan for critical problems affecting your systems, via alerts violations, issues, incidents, and anomalies.
- Overview: Find your most recent open, closed, and muted violations.
- Issues & activity: Review your most recent issues, incidents, and anomalies.
Detect problems in your system
Use the detect features to define the conditions in your system you want to be notified about, as well as to configure how anomalies are detected.
- Alert conditions (policies): Create new policies to group related conditions together. Also, lists the policies where your conditions are created and organized.
- Anomaly detection: Manage your anomaly detection configurations. An anomaly is a behavioral trend that doesn't match the historical data for your system. You can add or edit the configurations here.
Correlate the data coming into your system
Use the correlate features to define your data sources and to review and configure the logic that groups your incidents.
- Sources: Manage the data input sources you've chosen to analyze and be notified about. You can add new sources or configure existing ones.
- Decisions: Review your correlated incidents and make decisions on how to respond to them. You can also review, edit, and add decisions.
Enrich your notifications with useful metadata
Use the enrich and notify features to add additional metadata to your notifications, schedule when you don't want to be notified, and configure where your notifications get sent.
- Muting rules: Temporarily stop your alerts notifications.
- Workflows: Add more data to your notifications.
- Destinations: Configure where your applied intelligence notifications get sent.
Use Settings to review and manage your usage
Use the general settings page to review and manage your current incident intelligence usage.
Alerts (classic)
Alerts (classic) lets you manage events, incidents, and notification channels with the UI you're used to using.
- Events and incidents: Review alerts violations and other events.
- Channels: Review your alerts notification channels and to create new channels.